Is email secure for sensitive data? You are not the only one asking this tricky question.
Let’s take a look at telling statistics for 2022 across industries and see the importance of using only secure solutions for sharing confidential business information without data breach incidents:
- Healthcare organizations worldwide faced 1,463 cyberattacks per week, which is a 74% increase compared to 2021.
- Malware attacks on financial institutions increased by 35% in Q1 2022.
- The energy industry was the target of 10.7% of cyberattacks.
- At least 44 U.S. colleges or universities and 45 school districts suffered from ransomware attacks.
- In the second half of 2022, cyber attacks on governments surged by 95% globally.
And to top it all off, 29% of businesses reported losing a client due to a business email breach.
Why is email security so weak?
Email security is dangerously weak for multiple reasons, including the following:
- The open network infrastructure makes it easy for anyone with the internet to gain access to your confidential data, creating significant attack vulnerabilities.
- Outdated internet security protocols in many email providers make it easy to bypass them since they are not updated regularly, which may lead to identity theft.
- The risk of interception and exploitation due to insecure networks puts emails under additional pressure.
- The lack of end-to-end encryption in most email providers often compromises confidential information.
- Some users don’t take the necessary steps for email hacking prevention, such as password protection or two-factor authentication.
As a result, email security is far less reliable than other solutions for those who need to send sensitive information. So, the next time you ask yourself, “Is sending documents over email secure?” keep in mind the weaknesses mentioned and the dangerous types of email attacks we describe below.
Types of email attacks
There are over ten types of email attacks. They range from phishing to account takeovers designed to steal or disrupt data. Moreover, each attack type works differently; some even use social engineering techniques to deceive you into clicking on malicious content.
- Phishing scam. It is an internet scam in which thieves use email, text messages, advertisements, or other ways to impersonate reputable companies to steal personal information. Phishing attacks usually work by attaching a link that takes you to the company’s website to get your information. However, this website is fake, and the information you enter goes straight to the scammers.

- Man-in-the-middle attacks. It is a situation where a third party intercepts communications between two unaware individuals. Attacks commonly occur by establishing fraudulent public Wi-Fi networks in public locations such as coffee shops and malls. This way, the man in the middle can try to get private information or infect your devices with harmful software.
- Business email compromise. Malicious actors imitate colleagues, C-suite executives, or high-ranking authorities and deceive victims into depositing funds into the hacker’s bank account. The hackers may also use the senior official’s email account to carry out the attack. Thus, the email looks to be from a coworker or business partner most of the time.
Top examples of costly email attacks
Let’s take a look at some real-life examples of how cybercrime can be lucrative for criminals and how vulnerable organizations can be to these attacks.
| Facebook and Google | Between 2013 and 2015, Facebook and Google were duped out of $100 million due to a phishing effort. The attacker issued a series of bogus bills to a business impersonating Quanta, which both Facebook and Google paid. |
| Crelan Bank | Crelan Bank in Belgium lost $75.8 million due to a business email compromise (BEC) scam. The attack involved a phisher accessing a high-level executive’s account and directing employees to transfer money to their account. |
| FACC | Austrian aerospace parts maker FACC also lost money due to a BEC scam. The company announced a phishing attack where a fake CEO instructed an accounting employee to transfer $61 million. |
What information should not be sent via email?
Our investigation has shown that users should avoid sending the following data via email servers since they aren’t powered by email encryption and other sophisticated security mechanisms:
- Personal information: social security numbers, banking information, and addresses.
- Confidential information: trade secrets, employee data, or proprietary technology.
- Financial information: payment information, account numbers, and credit card numbers.
- Legal documents: contracts, court orders, or legal advice.
- Private conversations: emails are not for safe online communication; any information you send via email can easily be intercepted and read by anyone, including hackers.
So, is email safe for personal information of any kind? Due to the numerous factors listed above, it is obviously not secure enough. This is why you should only use well-protected business document storage to share sensitive information and ensure that only the intended recipient can access it.
4 reasons NOT to email confidential information that business owners should know
1. You may forget to encrypt a file
Software like Word, Excel, or Adobe have an encryption feature built into the program — many users are probably unaware of this feature, or they forget about it. This results in sending an unprotected file, which reaches the recipient’s email provider.
Imagine someone hacking into your inbox and stealing those files. This would result in collateral damage and a data breach that could have been avoided. Here you can learn more about file encryption with data rooms.
2. You may send the file to the wrong person
Even without someone hacking into your email inbox, the files could get into the wrong hands. Sending an email to the wrong addressee happens more often than you think. Sometimes it takes just a typo to send the files to the wrong recipient.
You may even accidentally click the email address of a competitor, sending them sensitive information that could prove detrimental to your business — all it takes is a simple misstep
3. Your email can be forwarded to a third party
After sending off your email to the recipient’s inbox, you may think that your files are safe, but there is nothing further from the truth.
Any email can be forwarded, and you have no control over it. You might try protecting your files by storing them in an online hosting service. However, you may forget to provide the intended recipient with the appropriate permission for access to those documents.
4. Your email may get compromised
There are many people online that are just waiting for you to make a mistake. They are sending misleading emails that might result in sending documents to the wrong recipient. According to Avanan Global Phishing Report, 1 out of every 25 branded emails is a phishing attempt.
It is not necessarily your fault for getting tricked, people phishing for sensitive information are masters at manipulation. As there is a visible increase in phishing and trojan attacks worldwide, it should be reason enough to reconsider your file-sharing solutions. A secure data room might be the key to solving your troubles.
Consider secure solution for sharing sensitive information — virtual data rooms
A virtual data room is a perfect solution if you need secure alternatives to email. This is because VDRs offer a safe, confidential, and compliant environment for file-sharing and privacy in digital communication powered by data leakage prevention mechanisms.
Specifically, the providers use 256-bit secure socket layer (SSL) encryption, making the storage virtually impossible for hackers to access. In addition, you can also manage user access and permissions, so you control who has access to your data and what they are allowed to do with it.
Data rooms also offer a wide range of features, such as document tracking, real-time audit trails, and the ability to set file expiration dates. It makes monitoring who accessed data and when simple.
Overall, data rooms are the most reliable business solution for those who want to send sensitive information securely. They provide the utmost security and a range of other virtual data room features to streamline and protect data management, including data room indexing, AI-powered redaction, and full-text search.
Top VDR providers for sharing sensitive data
Do you still wonder, “Is it safe to send confidential information in an email”? Make confident and intelligent business decisions instead – choose your best solution today!
Based on our observations, the best virtual data rooms for keeping your internet privacy and sensitive documents intact are as follows:
1. Ideals
SOC2-certified and GDPR-compliant Ideals makes data protection more straightforward than ever before. In particular, the solution provides 256-bit encryption with your own decryption key, granular permission settings, two-factor authentication, remote shred, eight levels of document access rights, and a fence view. With all this, Ideals ensures the safety of sensitive information management and helps businesses facilitate and protect document management workflow.
Ideals fence view feature:
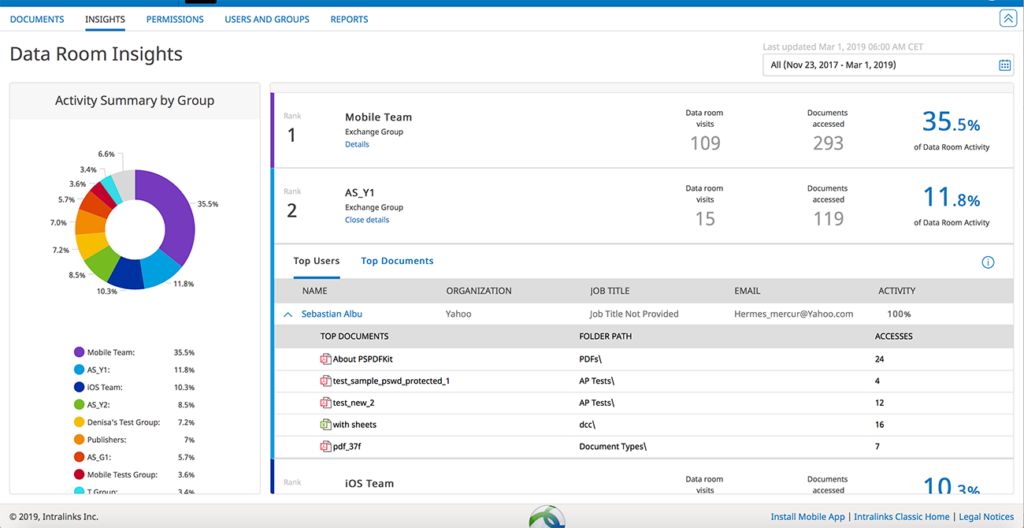
2. Intralinks
Intralinks is another leading service provider of virtual data room solutions. Its security features include permission management with 16 user roles, digital rights management, end-to-end encryption, and activity monitoring. Also, Intralinks automatically backs up all data stored within the storage and provides data recovery in case of a system crash or unexpected outage.
Intralinks activity monitoring feature:
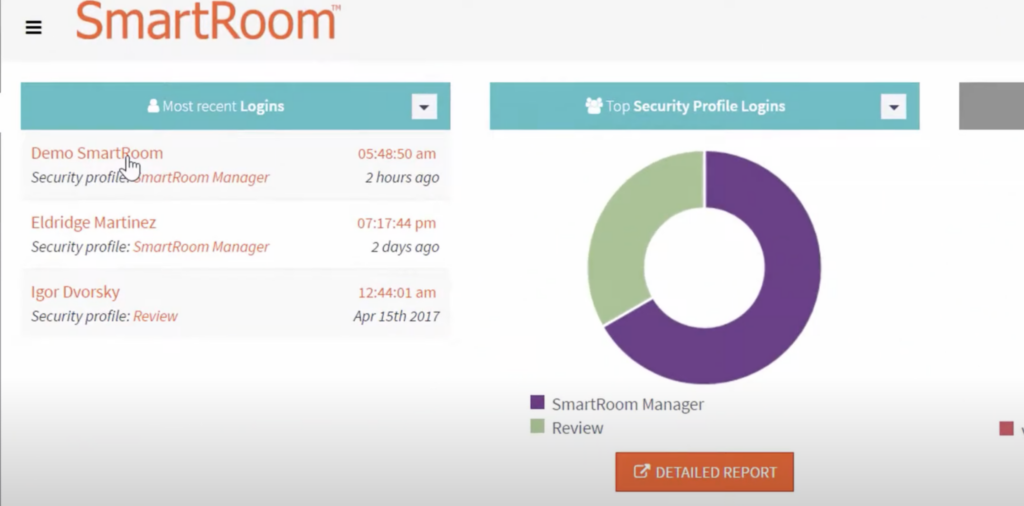
3. Smartroom
With Smartroom, you can rest assured of having encrypted messages and documents. Thus, the solution allows blocking access to a file even if a recipient has downloaded it, applying redactions to keywords and data patterns, monitoring data room activity, and sending files directly to your workspace from your email without risks.
Smartoom reporting feature:
Key takeaways
So, can sensitive information be emailed if encrypted? As you can see, email is unreliable and can’t offer both the sender and the recipient enough security, even if it does offer encryption.
So, choosing a trustworthy virtual data room to keep your data safe is the best option. A good VDR should have robust encryption protocols and critical features such as user authentication and access control so that only you decide how to manage your data.

